Table of Contents
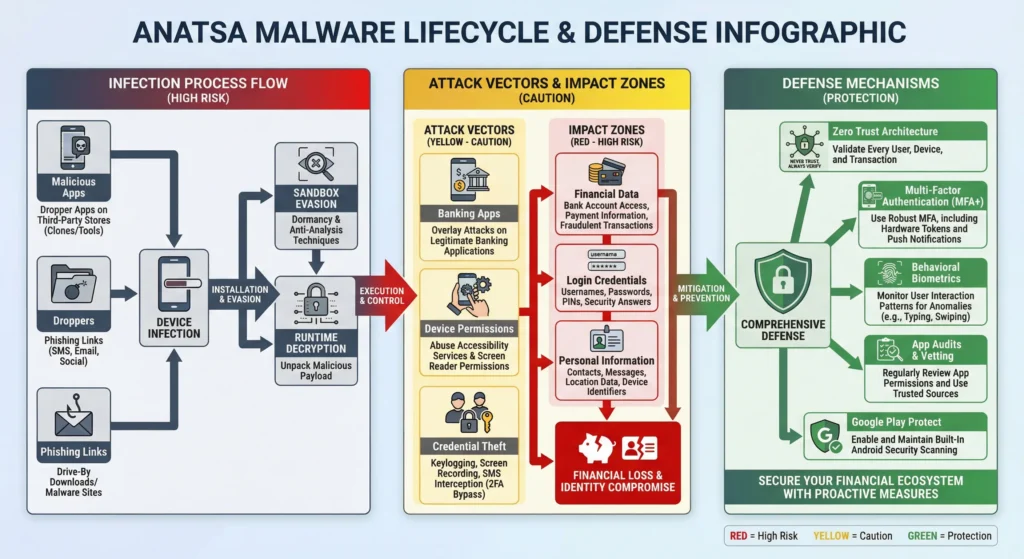
Anatsa Malware is a complex banking Trojan that can steal financial credentials, personal data, and two-factor authentication codes on android devices. It gets around security by droppers, runtime decryption, and sandbox evasion, as well as individual users and financial institutions. Users are advised to use Google play protect to resist it, update the apps, and review permissions, whereas banks have to use Zero Trust, MFA+, behavioral biometrics, and continuous monitoring. It is necessary to take proactive measures to avoid the loss of finances, reputation, and risk of regulation.
1. Malware Anatsa and Its Threat
Anatasa is a very complex banking Trojan that is set to rob sensitive financial data on the infected machines. It belongs to the category of malware but it mainly targets online banking credentials, credit card information, and personal data, a threat that is incredibly dangerous to an individual as well as a business. Its features are keylogging, screen capture, stealing two-factor authentication passwords, and tricking device permissions to provide unauthorised access to applications and accounts. Anatasa is usually passed through phishing e-mails, viral links, or trojanized software pretending to be normal software. After it is in place, it works silently in the background and it is therefore hard to detect and it keeps sending stolen information to the remote servers. The fact that the malware can bypass security controls and directly access the financial accounts is especially dangerous, which in most cases leads to identity theft, unauthorized transactions, and huge financial loss. The defense mechanisms that are necessary against this threat are vigilance, updated security software, and cautious online behavior.

2. How Anatsa Bypasses Google Play Security
The technique applied by Anatsa to bypass Google Play security is the layered and adaptive attack method which is uniquely created to avoid automated detection and manual review. The dropper model is one of its fundamental methods. Rather than directly installing the malicious code inside the application that is uploaded to Google Play, the attackers post a ostensibly innocent application, like a utility, a QR scanner, or even a productivity tool. This first application is not subject to a security check as it does not harbor any blatant malicious code. After installation and being trusted by users, the dropper then downloads or activates the actual malware at an external source.
Runtime decryption is another important technique. A malicious code is encrypted by Anatsa when at rest and the harmful code cannot be read when performing a static analysis. The malware decrypts when it is in memory only after the app is installed and running on a real device. This greatly constrains the efficiency of signature-based detection schemes, since no definite evil signature is pronounced to scan upon when submitting the app or when it is being executed prematurely.
Sandbox evasion is also used by Anatsa to prevent being detected by automated testing environment of Google Play Protect. Sandboxes commonly replicate behavior of users in the short term, yet Anatsa postpones malicious actions until a certain precondition is reached. These prequisites may include some period of time, user engagement in the application, physical location of device checks, or even the existence of the actual banking apps. In case of a lack of such signals the malware stays in inactive state and looks innocent during analysis.
Also, Anatsa uses the Android permissions slowly. It does not demand dangerous permissions at once which minimizes suspicion. It is socially engineered in the long run to grant accessibility and notification access, which would allow complete account takeover.
This droppers, runtime decryption and sandbox evasion allow Anatsa to constantly break into Google Play, infect millions of devices and remain unnoticed over a short period of time. It points to the rising complexity of mobile malware, and how a layered security is necessary beyond what app stores can offer.
3. Scale and Impact of the Anatsa Threat
Anaatsa has quickly become a mobile banking menace that has impacted thousands of devices around the world. Security researchers project that its dropper-based applications have been downloaded tens of thousands of times, usually under the guise of valid utilities or productivity programs. The malware is mostly aimed at the Android banking applications, with dozens of large banks and financial services being affected. Its covert nature can allow it to perform its activities without being detected in weeks and thus steal sensitive credentials, one-time passwords, and account data. Anatsa infections have also resulted in unauthorized transactions, identity theft, and have been associated with hundreds to thousands of dollars per victim losses, thus, it is one of the most destructive mobile banking Trojans currently being distributed. The extent and influence it brings out the importance of being proactive in mobile security and user awareness.
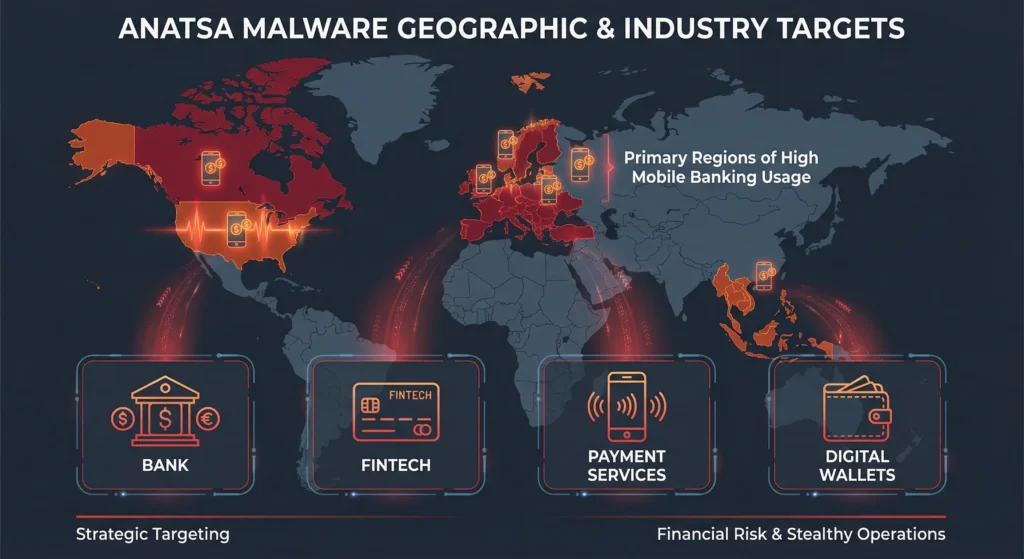
4. Target Analysis (Geographic): Geographic and Industry Target Analysis of Anatsa
Anatasa mainly focuses on the European, North American and some Asian users where mobile banking is very common and financial applications are well with the users. Although the primary victims are individual consumers, the malware has an indirect impact on financial institutions and fintech companies by targeting those that have popular banking apps. The main areas that will be affected are the banking, payment services and digital wallets whereby the breached credentials can be used to facilitate massive unauthorized transactions. This malware targets high-value areas and sensitive financial sectors, which increases its risk, whereby a breach can cause havoc to the banking operations, loss of customer faith, and massive financial losses to the users and institutions. Its targeting approach is geographical and sector-specific and this is a strategic tactic of maximizing the financial gain and be a stealthy approach.
5. C-Level Implications: Trust and Business Risk from Anatsa
To executives, Anatsa poses a considerable amount of reputational and operational risk. Customer privacy is easily compromised with breaches of their banking credentials, resulting in customer churn and brand erosion. Fiscal authorities and financial technology companies can also experience regulatory reviews and sanctions in case the violations are attributed to poor security measures. In addition to the short-term monetary losses, executives should bear in mind the strategic influence on the perception in the market, investor trust, and the position in the market. Lack of prevention of malware threats such as Anatsa may increase the risk of operation, damage relationships with customers, and diminish the credibility of leadership, which is why cybersecurity investment is one of the board-level priorities.
6. Contrarian Argument: Why Cleanup of Play Store is Not Enough
It is not enough to use Google Play cleanup as Anatsa uses the weaknesses inherent in the system in which the app is reviewed, and has more sophisticated methods of attack such as droppers, runtime decryption, and sandbox collusion. The automated detection and delayed threat response are structural bottlenecks that enable malware to live on the platform thus the importance of multi-layered security in addition to app store monitoring.
7. Strategies to be taken against Anatsa in the financial institutions.
Multi-layered security is the way that financial institutions should use to face threats such as Anatsa. A Zero Trust architecture will help mitigate the threat of unauthorized access because it will ensure that every device, user, or app is not implicitly trusted. Implementing multi-factor authentication (MFA+) will provide the extra security against credential theft. By adding behavioral biometrics, unusual user activity is detected in real time and allows responding quickly to a possible fraud. Institutions are also supposed to control the permission to access the apps to only grant access to privileges not required, which malware might have exploited. Constant security audits, employee training, and continuous monitoring of banking applications also help in fortification. With the integration of these strategies, the organizations can reduce financial losses, retain customer confidence, and react preemptively to advanced mobile banking malware attacks.
8. Recommended Actions for Users
The most effective security measures that users can take to prevent Anatsa would ensure that they update their OS and apps regularly, use Google Play Protect, and should not download products and services that are not trusted. Perform regular application audits to eliminate suspicious or unnecessary applications and audit application permissions to restrict access. The application of strong and unique passwords and multi-factor authentication on banking and financial applications is an added protection measure. It is important to be alert to any phishing and pop-ups and unsolicited messages. All these measures taken in advance will allow users to minimize the threat of infection and protect their valuable financial and personal information against viruses.
9. Conclusion
Anatsa is a risky threat of mobile banking, which uses the vulnerability of devices and advanced evasion measures and the trust of users to steal sensitive financial information. Individuals and financial institutions risk financial and reputational loss and legal investigation by the regulator in case of insufficient defenses. Multi-layered security, which includes a combination of Multi-Factor authentication, behavioral biometrics, App permission management, and continuous monitoring are much more focused on a forward-looking approach to security. On the part of the users, app audits, safe downloading, and vigilance are necessary. By taking these measures proactively, the organization will be resilient to the changing malware threats, enhance trust, and protect the financial ecosystems in the long run.
10. FAQ
What is the Anatsa malware, and how does it jeopardize the banking applications?
Anaatsa is an advanced banking Trojan that gathers the personal information, credit cards and logs of its targets through exploiting the vulnerabilities of the Android machines and banking applications.
What can I do to know whether my Android device has been infected with Anatsa?
The symptoms may be the abnormal behavior of the app, the appearance of unanticipated notifications, unauthorized transactions, or unfamiliar applications on your phone.
Does Anatsa fall under the protection of Google Play Protect?
Google Play Protect has an entry-level level of protection, and Anatsa aviation techniques such as runtime decryption and droppers can make it escape without being recognized.
How would you recommend banks to address the problem of Anatsa attacks?
Zero Trust architecture, multi-factor authentication (MFA+), behavioral biometrics, and stringent management of app accessibility should be implemented by banks to secure the customer accounts.
What is the way behavioral biometrics will save my accounts with Anatsa?
Behavioral Biometrics identify abnormal user actions (pattern of typing, pattern of navigation) and therefore detects fraud quickly and mitigates unauthorized access by the offender even after stealing credentials.

Muhammad Asif is the Founder and Growth Engineer at WebNextSol, with 5 years of experience building AI-powered systems that help businesses save time, generate leads, and grow. He combines expertise in WordPress, automation, cloud architecture, and SEO to deliver practical, results-driven digital solutions.


